With the rise in the use of Microsoft 365 cloud services, these accounts have become very popular targets for cybercriminals. We have seen and heard directly from some clients that they have experienced a surge in attempts via phishing, in particular. These attacks are becoming more sophisticated as they frequently gain prior information about the organizations before the phishing attack, making them much more believable whether by email, text, or phone.
With millions of organizational accounts potentially vulnerable to preventable compromise each year, Microsoft worked with partners and customers in the creation of their Security Defaults*.
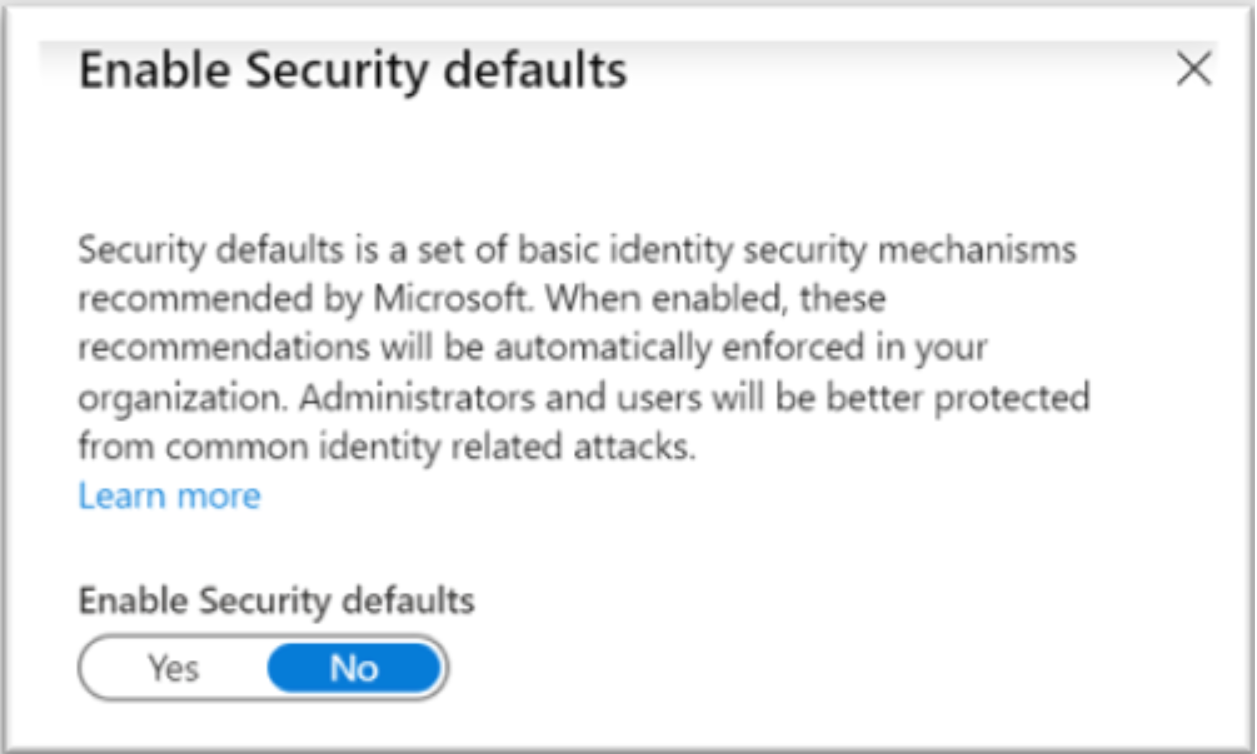
Security Default Features
Microsoft is making Security Defaults available to everyone, with no extra cost to your MS365 subscriptions.
If your organization owns Microsoft 365, you have the right to turn on your Security Defaults. When implemented, they do the following:
- Requires all users to register for Azure AD Multi-Factor Authentication.
- Requires administrators to always perform multi-factor authentication.
- Blocks legacy authentication protocols.
- Requires regular users to perform multi-factor authentication when necessary. Protects privileged activities like access to the Azure portal.
We advise proceeding with caution when implementing Security Defaults. It is a powerful tool that affects many settings through the suite of Microsoft applications at the user level and the administrator level. These are features best implemented by your Microsoft Administrator.
Microsoft Admins can start to understand the Security Default fundamentals HERE.
Ready to Increase Your Security Posture?
If you’re interested in increasing your Microsoft 365 security but you don’t know how or where to start, please contact us. Don’t go I.T. alone.
Our Microsoft Professionals are here to help with Security Defaults configuration and implementation. Get started by emailing us at info@pccorp.com.
* Microsoft’s telemetry identifies that more than 99.9% of organization account compromises could be stopped by simply using MFA and that disabling legacy authentication correlates to a 67% reduction in compromise risk (and completely stops password spray attacks, 100% of which come in via legacy authentication).