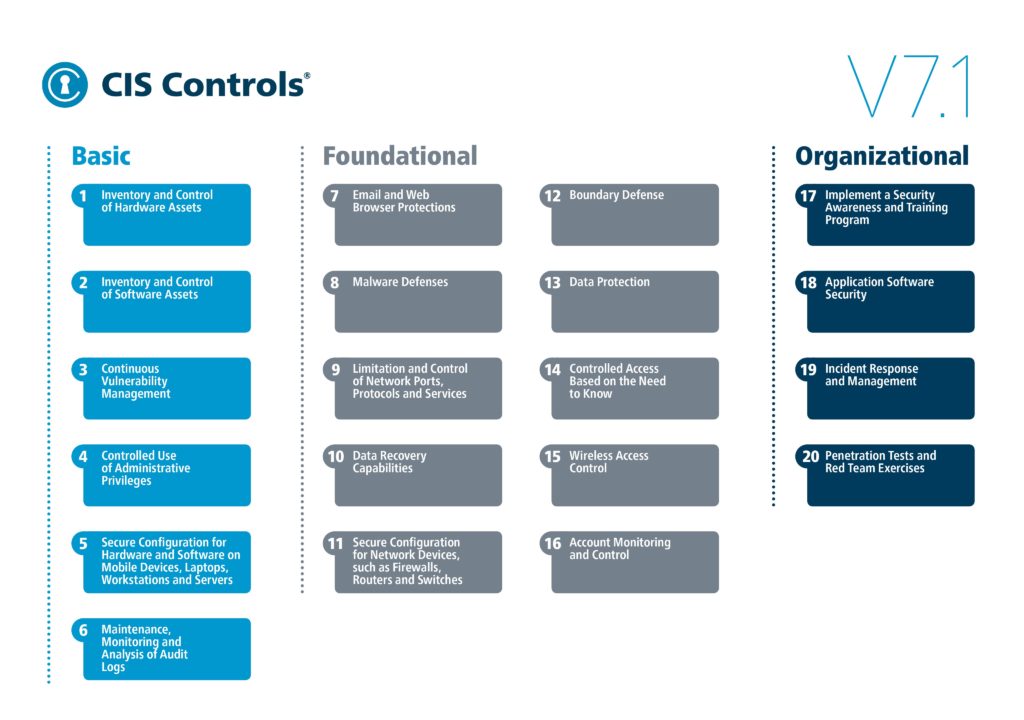
As security challenges evolve, so do the best practices to meet them. To stay up to date, many I.T. security professionals refer to the top 20 CIS Critical Security Controls (CSC) list, published annually by the Center for Internet Security (CIS). This is a ‘Top 20’ list that can help organizations better defend against known attacks as it distills key security concepts into actionable controls to achieve a greater overall cybersecurity defense.
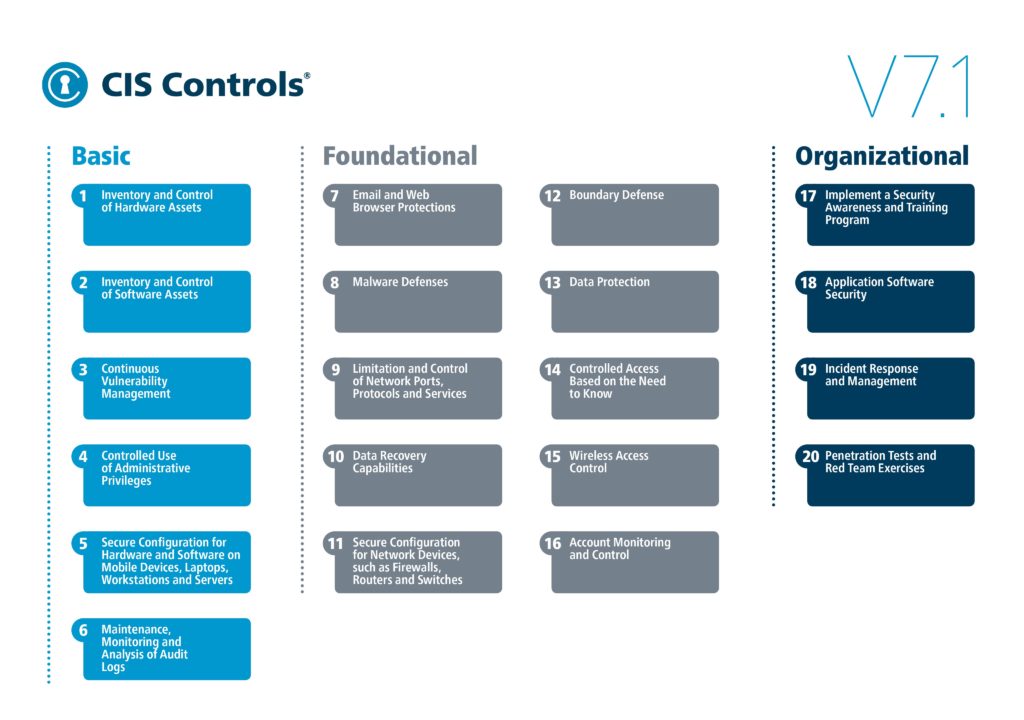
But as with any action list, it is difficult to execute all the items at once. So, which of the top 20 CIS controls above should you be looking at first? According to Roger A. Grimes, KnowBe4’s Data-Driven Defense Evangelist, his top 5 CIS controls to implement are:
- Implement a security awareness and training program
- Continuous vulnerability management
- Controlled use of administrative privileges
- Maintenance, monitoring and analysis of audit logs
- Incident response and management
1. Implement a security awareness and training program
Security is not only a technology issue. People also play a critical role your network’s safety. By training your employees to understand the warning signs and to follow best practices, they can drastically reduce the likelihood of an attack.
2. Continuous vulnerability management
By regularly scanning your environment for vulnerabilities and missing patches, and automating as much of that patching as is possible, your computer security risk will drop dramatically.
3. Controlled use of administrative privileges
Want to stop the worst malicious abuses of your computers and network? Stop the bad guy from getting administrator and root. And that means:
- Minimize the number of administrator users and admin accts.
- Set high securities to high for administrator account access ex) include multifactor authentication to log on
- Monitor administrator account access, flag heavy use, and investigate
4. Maintenance, monitoring and analysis of audit logs
Analyzing your event logs for you can help to identify suspicious events in your environment. Invest in a good security information event management (SIEM) to do the heavy lifting of reviewing data, then all you should need to do is investigate the problems it identifies.
5. Incident response and management
Having an effective incident response plan in place will help you recover should you fall victim to an attack. The better and quicker incident response investigation and remediation happens, the less damage a cyberattack can cause to your business.
For organizations looking to improve their security posture and improve their defences, the CIS Critical Security Controls are a great starting point to reduce your risk of exposure and mitigate the severity cyberattacks.
We are here if you have any questions or need assistance with your security controls. Our I.T Managed Services team can help you get your security environment on track. We make I.T. easy. Just ask.
Article Resources:
https://www.csoonline.com/article/3438119/the-5-cis-controls-you-should-implement-first.html?upd=1569790956404
https://www.cisecurity.org/press-release/cis-introduces-v7-1-of-cis-controls-featuring-new-implementation-groups/
https://www.csoonline.com/article/2124604/what-is-siem-software-how-it-works-and-how-to-choose-the-right-tool.html